We recently replaced our existing router with a Meraki MX65w Security Appliance. While Meraki does have multi-factor authentication to log into the cloud controller, we were disappointed to find out that they do not have multi-factor authentication for client VPN. However, there are third-party solutions that can be used to provide multi-factor authentication for client VPN. These third-party solutions can be found on Meraki’s website below.
https://documentation.meraki.com/MX-Z/Client_VPN/Using_Two-Factor_Auth_with_Client_VPN
We chose to use Windows Azure Multi-Factor Authentication (Azure MFA) Server. The Azure MFA Server is installed on a Windows 2012 Server acting as a Domain Controller. Unfortunately, the set-up and configuration of Azure MFA with Meraki Security Appliance is not well documented. Below are some useful tips from our experience with setting this up.

- By default, the Client VPN timeout on the Meraki Security Appliances is 15 seconds. For there to be enough time for the authentication to complete this must be extended. To extend this you will have to open a support case via the Meraki dashboard and ask to have it extended. Azure recommends this being at least 60 seconds.
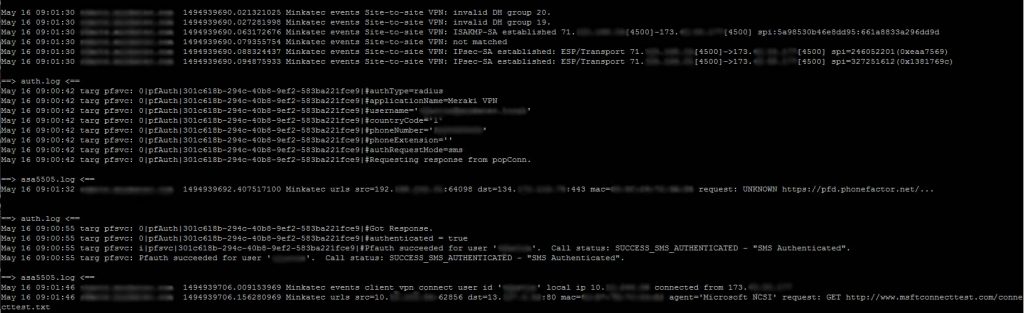
- Logging is very important. Both the Meraki Security Appliance and the Azure MFA server have the capability to configure syslogs. This is very useful as it shows the communication between the two devices and can help pinpoint where the issue lies. Below is a copy of our logs once we had this set-up properly.
- Be persistent and know when to walk away and take a break.
Hope these tips help!