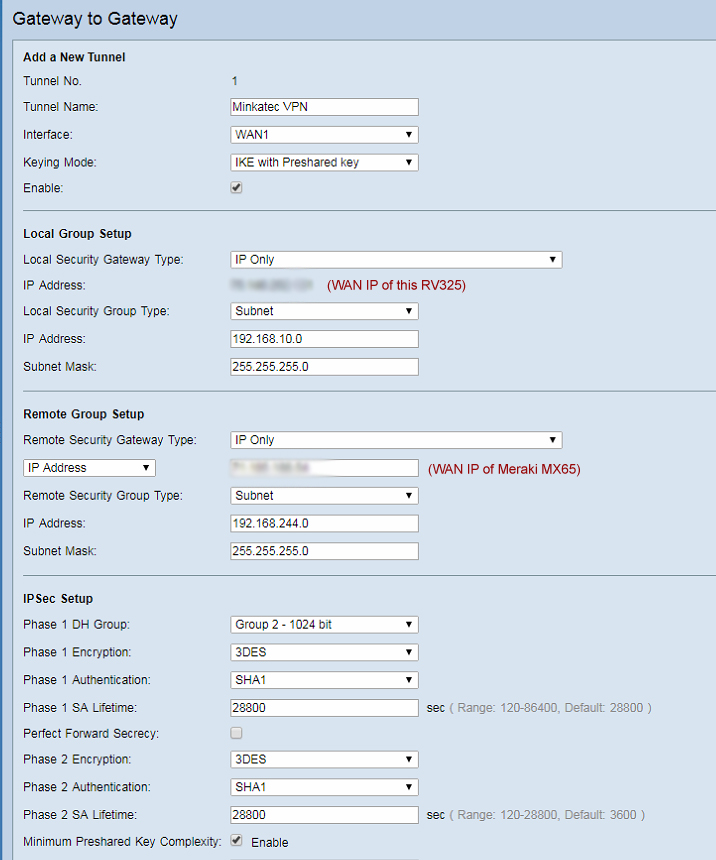
We recently had the need to establish a Site to Site VPN connection with our Meraki MX65w security appliance. Meraki security appliances have the option to establish a Site to Site VPN connection to other security appliances as well as other third-party routers. In our scenario, we successfully configured a […]
Tim
We recently replaced our existing router with a Meraki MX65w Security Appliance. While Meraki does have multi-factor authentication to log into the cloud controller, we were disappointed to find out that they do not have multi-factor authentication for client VPN. However, there are third-party solutions that can be used to […]
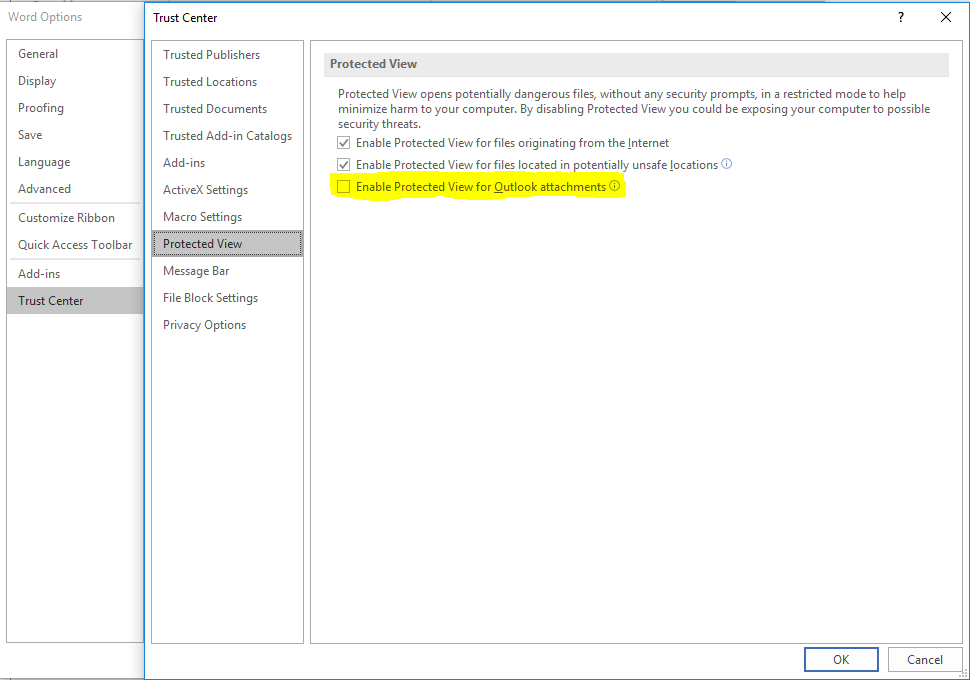
Microsoft recently added a new feature that by default prevents the opening of Microsoft Word, Excel, and PowerPoint files sent as attachments in Outlook. When attempting to open, users may receive error messages like the one below. These error messages usually do not define the problem. For example, looking at […]
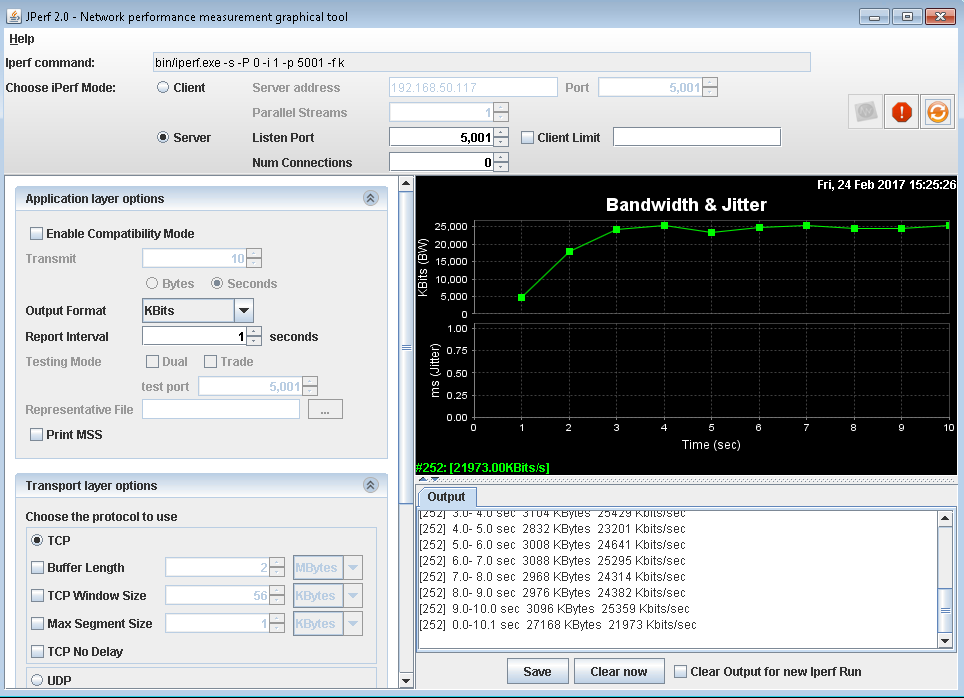
Recently we found a great tool to test network performance called JPerf. JPerf is a GUI that builds and run the IPerf network performance measurement tool command for you, all you have to do is input the required fields. Using JPerf is very simple. First, you will need two machines, […]
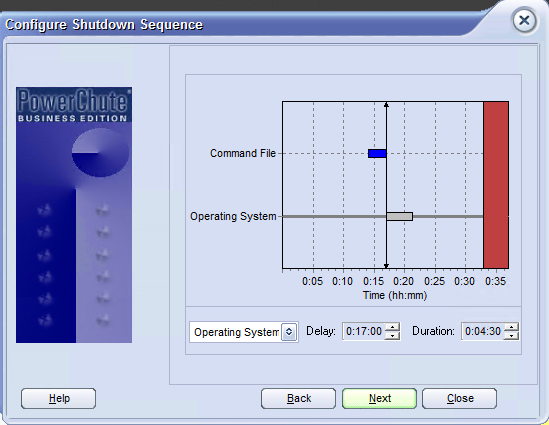
If you are on a budget and running VMware ESXi without paying for VMware license and are looking for safe way to shutdown VMs during a power failure then look no further. We have found a way to safely suspend all VM’s running on an ESXi host in the case […]