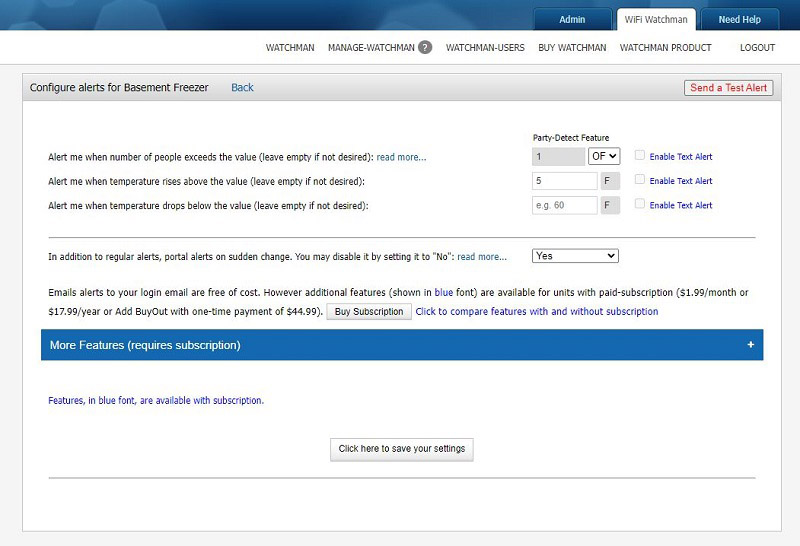
Have a freezer in the garage? How much would it cost you if it stopped working? Have a vacation house? Surely you want to monitor its temperature to avoid frozen pipes in the winter. Connect this inexpensive monitor to your WiFi and you’ll get e-mail alerts if thresholds are exceeded. […]
Jim
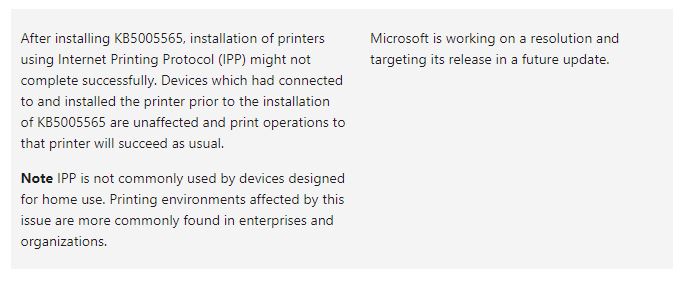
Since Windows Updates were released Tuesday, we’re receiving an increasing number of calls from customers who are unable to print. So far, in all cases, the printers are shared from a server in a non-domain environment. Uninstalling 2021-10 Cumulative Update for Windows 10 resolves the issue (KB5006670). After uninstalling KB5006670, […]
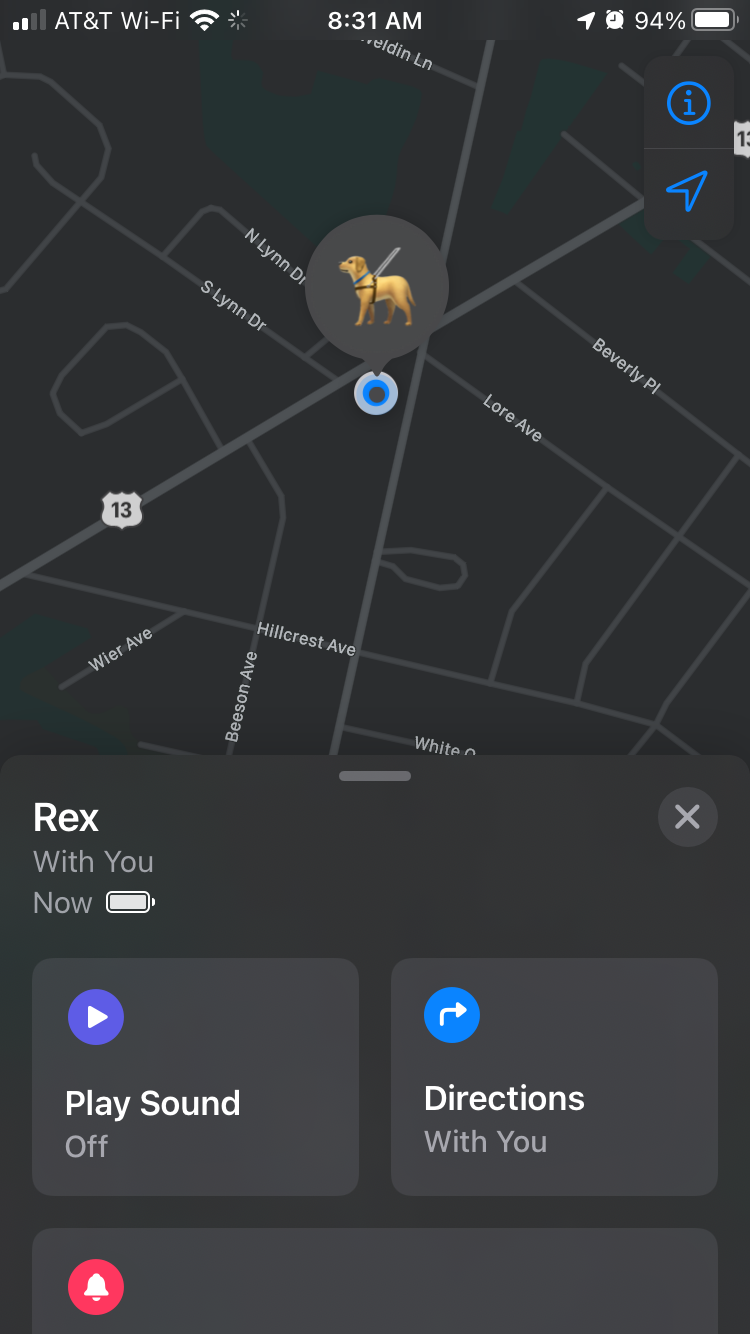
Apple has consistently said that the AirTag is meant to track items, not people or pets. The biggest downside is your pet needs to be in range of a device in the Find My network so its location can be tracked. That means it’s not perfect, OK, I’m good with […]
Our security cameras caught these tires rolling down Philadelphia Pike. Luckily no one was hurt. Found one next day near the bottom of the hill.
I was an early adopter of Nest Protect Smoke and CO Alarms. I installed four of them in my house 7-years ago. Unfortunately, the carbon monoxide alarms expire since their sensors have a limited lifespan. 1st gen Nest Protect has to be replaced after 7 years. Google is a technology […]
We’ve recently seen increased interest from business owners wanting to provide remote access for their employees. What’s the most cost effective and secure way of doing it? Remote Desktop Software such as LogMeIn Pro, TeamViewer, and GoToMyPC are good options when you have 2 or less computers to access remotely. All are easy […]